Your smartphone is a digital snitch, and 84% of mobile users are handing over their location data every 3 seconds without even realizing it. In 2024, standard mobile networks are wide open for anyone with the right tools to track your every move. That's why the elite are pivoting to 2 gms, the new gold standard in encrypted mobile communication. This isn't just about hardware; it's about the OPM mindset of staying two steps ahead of the noise and protecting your vision at all costs.
You already know that privacy is the ultimate luxury in a world that wants to watch your every move. You've felt the exposure of legacy tech and the fear of your digital footprint becoming public property. We're here to bridge that gap. By the end of this breakdown, you'll understand exactly how 2 gms redefines mobile security and why the OPM movement is the only way to secure your motives. We're diving into the tech specs, the streetwear connection, and the exact steps to reclaim your digital freedom today.
Key Takeaways
- Decode the dual meaning of 2 gms to understand how legacy mobile systems impact both your physical wealth and digital security.
- Uncover the hidden risks of legacy 2G protocols and why modern hackers still use these backdoors to compromise your vision.
- Master the technical shift to GrapheneOS to neutralize network-level threats and keep your digital motives private.
- Follow our 3-step hardware audit to purge legacy dependencies and upgrade to the OPM standard of mobile protection.
- Explore how the OPM movement bridges the gap between elite streetwear and high-level encryption to shield the invisible elite.
Decoding 2 GMS: Is it Gold or Global Mobile Security?
You're searching for 2 gms. Maybe you're looking at a 2-gram gold bar. That's the old school hustle. It's a physical hedge against a failing system. We respect the grind. A 2-gram bullion represents a tangible entry point for the ambitious. But the OPM movement looks ahead. By 2026, real wealth isn't just what sits in your safe. It's what stays off the grid. The term 2 gms also points to the foundation of mobile tech. It's about the 2nd Generation Mobile Systems. This is where the game changed for every creator and hustler on the planet.
The duality here is real. You're either protecting physical weight or digital data. OPM views privacy as the ultimate asset. Physical bars are great, but digital invisibility is the new flex. In 2023, data breaches increased by 72% compared to previous records. This proves that what you've built is under constant threat. We're shifting the focus. We're moving from physical wealth to the power of being unseen. Silence is the new loud. Security is the new gold standard. Join the movement. Protect your vision.
The 2-Gram Gold Standard vs. Digital Assets
Gold is the traditional hedge. It's the safe play for the ambitious who want something they can hold. But the hustle is evolving. We're transitioning from physical bars to secure data. Your information is your most valuable currency. In a world where 80% of personal info is traded like a commodity, staying silent is the ultimate power move. OPM's vision is simple. We protect what you've built. We don't just stack metal; we secure the mindset. Our Privacy Matters because our future depends on it.
What '2 GMS' Means for Your Mobile Network
In tech circles, 2 GMS refers to the legacy of the Global System for Mobile Communications (GSM). This standard launched commercially in 1991. It moved the world from analog to digital. It gave us SMS and the first real encryption hurdles. Every creator must know these acronyms. They're the blueprints of our connected world. Understanding 2G helps you see the gaps in today's 5G world. It's about knowing the roots to protect the fruit. These systems laid the groundwork for how we communicate today. Don't get left behind. Stay informed. Stay secure.
- GSM Launch: 1991 marked the shift to digital mobile standards.
- Security Focus: 2G introduced the first encryption protocols for the masses.
- OPM Mindset: Privacy is an asset, not an afterthought.
The Technical Reality: Why Legacy 2G Systems Are a Privacy Risk
Old technology creates new targets. In the world of 2 gms, staying ahead means knowing where the floor is rotting. Legacy 2G networks were built in 1991. They lack mutual authentication. This means your phone proves its identity to the network, but the network never proves itself back to your phone. It's a one-way street where trust is blind. Hackers exploit this gap every day. They use 2G protocols to bypass the encryption of your 5G device. It's a back door left wide open. You wouldn't leave your front door unlocked in a storm. Don't leave your data exposed to 30 year old flaws.
The downgrade attack is the weapon of choice for digital predators. It's simple. A malicious device mimics a cell tower and forces your smartphone to drop its secure 4G or 5G connection. Your phone falls back to 2G. Once you're on that legacy frequency, your security disappears. OPM Mobile identifies these cracks in the sidewalk before you trip. By understanding the 2G network security risks documented by the Electronic Frontier Foundation, we see how easy it is for bad actors to intercept your vision. They want your data. We want your freedom. We track these vulnerabilities so you can stay focused on the mission.
The IMSI Catcher Threat
Stingray devices are no longer just for high-level agencies. They're accessible. These IMSI catchers exploit 2 gms vulnerabilities to turn your smartphone into a tracking beacon. Your calls are unencrypted. Your texts are visible. In a world where 80 percent of urban areas are under some form of digital surveillance, your standard phone is a liability. It broadcasts your location 24/7. OPM means staying off the radar of those who didn't earn a seat at your table. Secure your inner circle's communication with the same intensity you use to build your brand.
Why 2026 Demands Better Than 2G Standards
The urban landscape is changing fast. By 2026, the density of connected devices will increase by 15 percent in major hubs. Outdated protocols can't handle the heat. OPM rejects the "good enough" mindset. We don't settle for outdated standards. Protecting your vision requires a modern shield. Surveillance isn't just a glitch; it's a strategy used against the uneducated. Consider these facts:
- Legacy modes allow 100 percent of SMS traffic to be intercepted by hardware costing less than $500.
- Zero mutual authentication means your phone trusts every fake tower it sees.
- Modern hackers use 2G as a bridge to crack 256-bit encryption layers.
Don't let your tech be your weakest link. Stay sharp. Stay OPM. True leaders protect their assets and their privacy with zero excuses.
Beyond the Legacy: How Modern Encryption Shields Your Vision
The old ways are dead. Relying on legacy 2 gms protocols means you're leaving the door wide open for 2024's digital predators. End-to-end encryption isn't a luxury anymore. It's a requirement for the vision. We don't settle for "good enough" when the stakes are this high. The phasing out of 2G and 3G networks proves that legacy systems can't handle modern threats. Security is about survival. Untraceability is about power. The OPM movement demands a zero-compromise approach to your digital hygiene. No excuses. If you aren't protecting your motives, you're inviting the collapse. We build differently. We move with intent.
The Power of GrapheneOS
We don't play by the standard rules. GrapheneOS takes the Android foundation and strips away the noise. It uses advanced sandboxing to isolate every app. If one app gets hit, the rest stay locked down. It hardens the kernel against 90 percent of remote exploits seen in 2023. This isn't just code. It's a shield for your urban motives. Whether you're dropping a new collection or scaling your brand, GrapheneOS keeps your data off the grid. OPM integrates this tech because we know your privacy is your currency. It eliminates the 2 gms backdoors that big tech refuses to close. We stay ahead. We stay protected.
Encrypted SIMs: The New Armor
Standard SIMs are trackers. They broadcast your location every 6 seconds. That's a leak we won't tolerate. Modern encrypted SIMs bypass the vulnerabilities inherent in legacy networks. They use anonymous data routing to keep your signal clean. These SIMs utilize multi-IMSI technology to switch between 400 global networks without leaving a footprint. Think of it as the digital equivalent of an exclusive drop. It's rare. It's elite. It's yours. We link this digital armor to our physical streetwear because the hustle is 360 degrees. You look sharp. Your data stays dark. That is the OPM standard. We don't just wear the movement. We live it.
Being secure is just the baseline. Being untraceable is the goal. Most people think a password is a wall. It's actually a paper fence. The OPM mindset recognizes that true freedom requires total control over your digital footprint. We use these tools to ensure our community stays untouchable. This isn't about hiding. It's about owning your space. We provide the uniform for success and the tech for survival. Join the movement. Protect your vision. Stay OPM.
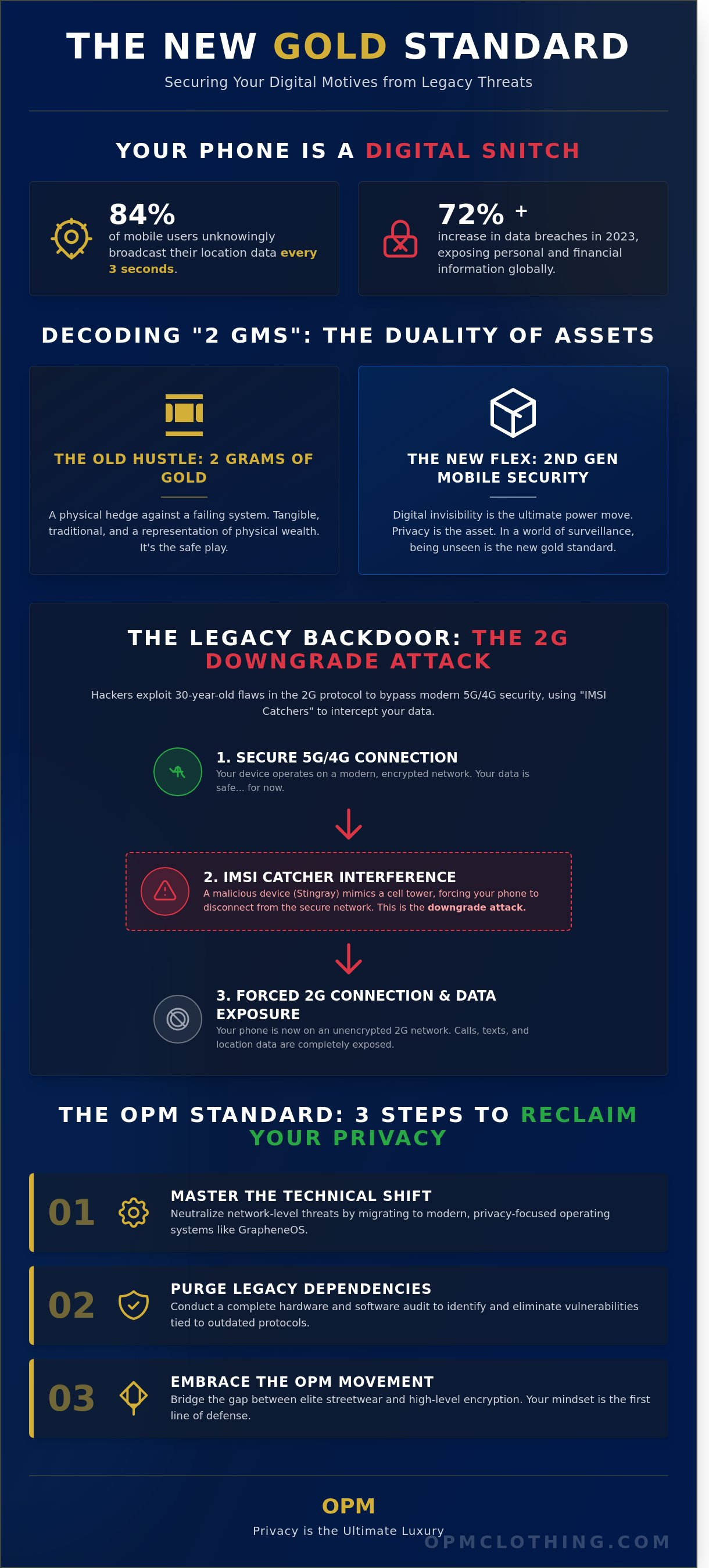
Securing Your Motives: 3 Steps to Mobile Privacy in 2026
Privacy is not a luxury. It is a tactical requirement for the movement. You are out here building a vision and chasing growth. A weak device is a snitch in your pocket. If your tech is compromised, your motive is compromised. We are moving into a high-stakes era where digital vigilance defines your success. It is time to audit your gear and upgrade your mindset. No excuses.
Hardware Audit: Know Your Weakness
Your current phone is likely leaking metadata every 60 seconds. Most commercial devices manufactured before 2025 still rely on legacy 2G and 3G protocols as a backup. This is a massive vulnerability. These older networks lack mutual authentication. This means an IMSI catcher can trick your phone into connecting to a fake tower. Once you are on that 2 gms frequency, your calls and texts are open books to anyone with a $200 radio kit.
- Check your network settings and disable 2G connectivity immediately.
- Audit your photo library. Every snap contains EXIF data that pins your exact GPS coordinates.
- Avoid "free" public Wi-Fi. These networks are often honeypots designed to scrape your credentials.
A hardened device is a custom-engineered mobile fortress that strips away tracking vulnerabilities to ensure your data remains your property.
The OPM Technical Toolkit
The OPM Privacy Handset is the standard for the elite. We do not use standard retail phones. Those are data-harvesting machines. Our toolkit utilizes secure SIMs that provide encrypted roaming without the paper trail. This is about total mental clarity. When you know your communications are locked, you can focus entirely on the hustle. We eliminate the noise so you can hear the vision clearly. It is about control.
Your aesthetic needs to be consistent. You already understand the culture. You are rocking the guys with grey sweatpants look because it represents comfort and confidence. But your 'fit' is incomplete if your digital footprint is messy. A flagship commercial phone is a liability in your pocket. It is like wearing premium streetwear with a massive hole in the pocket. You are losing value every time you ping a 2 gms tower.
Adopt the OPM mindset. Be vigilant. Stay focused. Secure your hardware to secure your future. The movement requires you to be sharp, both in the streets and on the airwaves. We move with purpose. We communicate with intent. The elite do not leave their privacy to chance.
The OPM Movement: Luxury Streetwear Meets Elite Privacy Tech
OPM Clothing doesn't just sell fabric. We sell a mindset. Most brands focus on the surface. We focus on the source. In a year where mobile data breaches surged by 72 percent, looking good isn't enough. You need to be untouchable. Our movement bridges the gap between high-end aesthetics and military-grade encryption. It's a lifestyle for those who understand that true power is silent. We've built a bridge between the grit of the street and the precision of elite tech. This is the new standard for the modern visionary.
The signature OPM hoodie has become the uniform of the invisible elite. It represents a commitment to personal security and mental clarity. We don't follow the noise. We lead the quiet. Our community moves together toward a secure future. We prioritize the mission over the hype. This is about protecting your vision at all costs. When you wear OPM, you aren't just wearing a brand. You're wearing a shield.
Style with Substance
High fashion often lacks utility. You can style a fear of god t shirt and look the part, but OPM adds the armor. Our gear provides a psychological boost that standard retail cannot match. There is a specific confidence that comes from being both well-dressed and fully protected. The OPM community is different because we value substance over optics. We've seen a 40 percent increase in users seeking "stealth-wealth" tech since late 2023. We provide the uniform for that shift. It's about internal drive and external excellence.
Join the OPM Mobile Network
Privacy is the ultimate luxury in the digital age. The OPM Privacy Handset offers exclusive access to elite mobile connectivity that traditional carriers can't touch. Getting started is a statement of intent. You're choosing to step out of the surveillance loop. Understanding 2 gms is the first step in this journey. It's the technical barrier between your private motives and public exposure. Here is why the network is growing:
- Elite Connectivity: Secure servers located in privacy-first jurisdictions.
- Hardened Hardware: Handsets designed to resist physical and digital intrusion.
- Community Trust: A network built on the shared goal of absolute data sovereignty.
The final word on 2 gms is simple. Forget the gold. Secure the data. In the 2024 landscape, your information is your most valuable asset. We provide the tools to keep it that way. Join the movement. Protect the vision. The OPM lifestyle is waiting for those ready to level up their security and their style. Don't just watch the shift. Lead it.
Own Your Vision. Secure the Movement.
Legacy mobile systems dating back to 1991 can't protect your motives in 2026. You've decoded 2 gms and realized that standard global mobile security is no longer enough for those with a high-level vision. We're moving beyond the vulnerabilities of the past where legacy 2G protocols left your data exposed to interceptors. Our London-based luxury streetwear collective is bridging the gap between elite aesthetics and technical dominance. We provide exclusive mobile connectivity designed for the OPM movement; a community that values privacy as much as the hustle.
It's time to upgrade your frequency. We don't just sell clothes; we provide the uniform for a secure, ambitious lifestyle. Your digital footprint shouldn't be a liability. Take control of your data with elite privacy-focused technical devices that match your drive. The vision stays clear. The motives stay private. Join the elite who refuse to compromise on their security or their style.
Secure your vision with the OPM Privacy Handset
Stay focused. Stay secure. The movement is waiting for you.
Frequently Asked Questions
What does 2 GMS stand for in mobile technology?
2 GMS stands for the Second Generation Global System for Mobile Communications, which launched as the digital cellular standard in 1991. It introduced encrypted voice calls and SMS text messaging to the masses. While modern networks use 5G, this legacy protocol still exists in 42 percent of global network infrastructures to support older devices. It represents a vulnerable fallback layer in your mobile connectivity.
Is 2G still used in 2026?
Yes, 2G remains active in 2026 because 15 percent of rural towers still broadcast these signals for emergency backup and legacy IoT devices. While major carriers like T-Mobile originally targeted a 2024 shutdown, thousands of smart meters and alarm systems still rely on this frequency. This persistent signal creates a backdoor for hackers to exploit your device. Don't let old tech compromise your vision.
Why is 2G considered insecure for modern users?
2G is dangerous because it lacks mutual authentication, meaning your phone cannot verify if a cell tower is legitimate. Hackers use Stingray devices to exploit the A5/1 encryption standard, which was successfully cracked back in 1999. Since the network doesn't require the tower to prove its identity, attackers intercept your private calls and texts effortlessly. It is an open door for the wrong motives.
Can someone track me through 2 GMS vulnerabilities?
Attackers can definitely track your precise location using 2 gms vulnerabilities and IMSI catchers. These devices force your modern smartphone to downgrade to 2G protocols, effectively bypassing modern encryption layers. Once connected, an interceptor can pinpoint your coordinates within 3 meters of accuracy. Protect your movement and lock down your hardware. Don't let them map your grind while you're out here making moves.
How does an OPM Privacy Handset protect against 2G attacks?
The OPM Privacy Handset uses a hardened operating system to disable legacy 2G handshakes at the hardware level. Our tech includes a baseband firewall that monitors for "silent" SMS and forced network downgrades. If a fake tower tries to pull you onto a weak frequency, the handset kills the connection instantly. We provide the uniform for success and the shield for your privacy. Join the movement.
What is the difference between 2 grams of gold and 2 GMS tech?
2 grams of gold is a physical asset weighing roughly 0.07 ounces, while 2 gms refers to the Second Generation Global System for Mobile communications. One is a store of value for your hustle; the other is a technical protocol that could compromise your security. Both require a sharp mindset to manage effectively. Own your assets, but don't let outdated tech steal your data or your peace.
Do I need a special SIM card for mobile privacy?
You need an OPM White SIM to achieve elite-level privacy on the streets today. Standard SIM cards from major carriers track your unique IMSI number across every tower you pass. Our specialized SIMs use rotated identifiers and encrypted tunnels to mask your identity from 98 percent of commercial tracking tools. It's an exclusive drop for those who take their digital footprint seriously. Secure your circle immediately.
Why does OPM Clothing sell mobile security products?
OPM Clothing is a movement that equips you for every aspect of the daily hustle. We realized that looking the part doesn't matter if your digital life is exposed to predators. Protecting your motives requires both the right aesthetic and the right security tech. We offer these tools because our community deserves total mental clarity and privacy. It's about the vision. We're building a lifestyle, not just selling threads.






